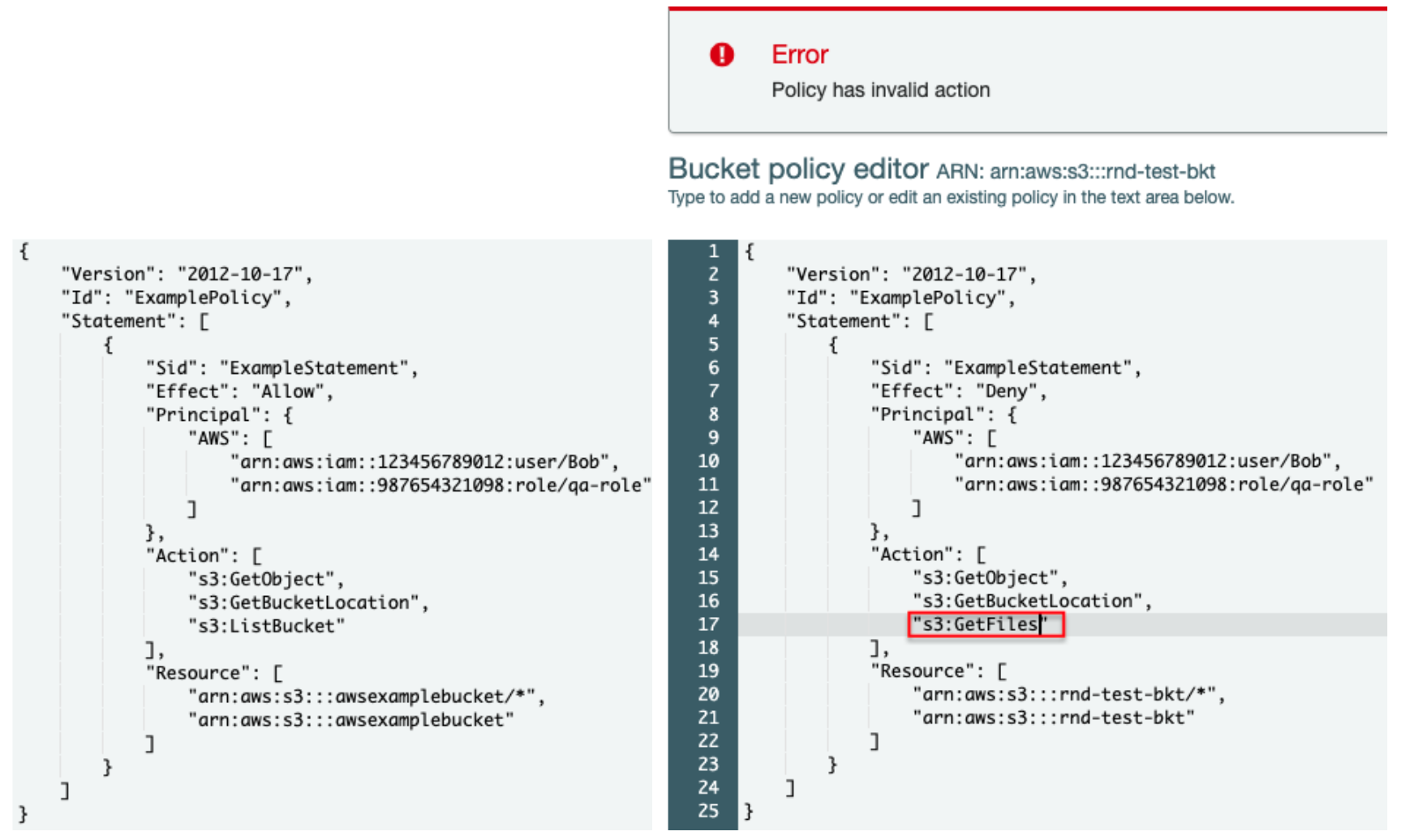
How to use resource-based policies in the AWS Secrets Manager console to securely access secrets across AWS accounts | AWS Security Blog

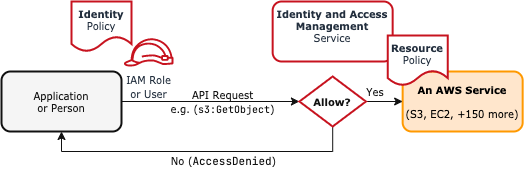
Ben Kehoe on Twitter: "Relevant policy evaluation diagram. Resource policy allows short-circuit the decision before permissions boundaries are evaluated. https://t.co/9EPqorfQv0" / Twitter

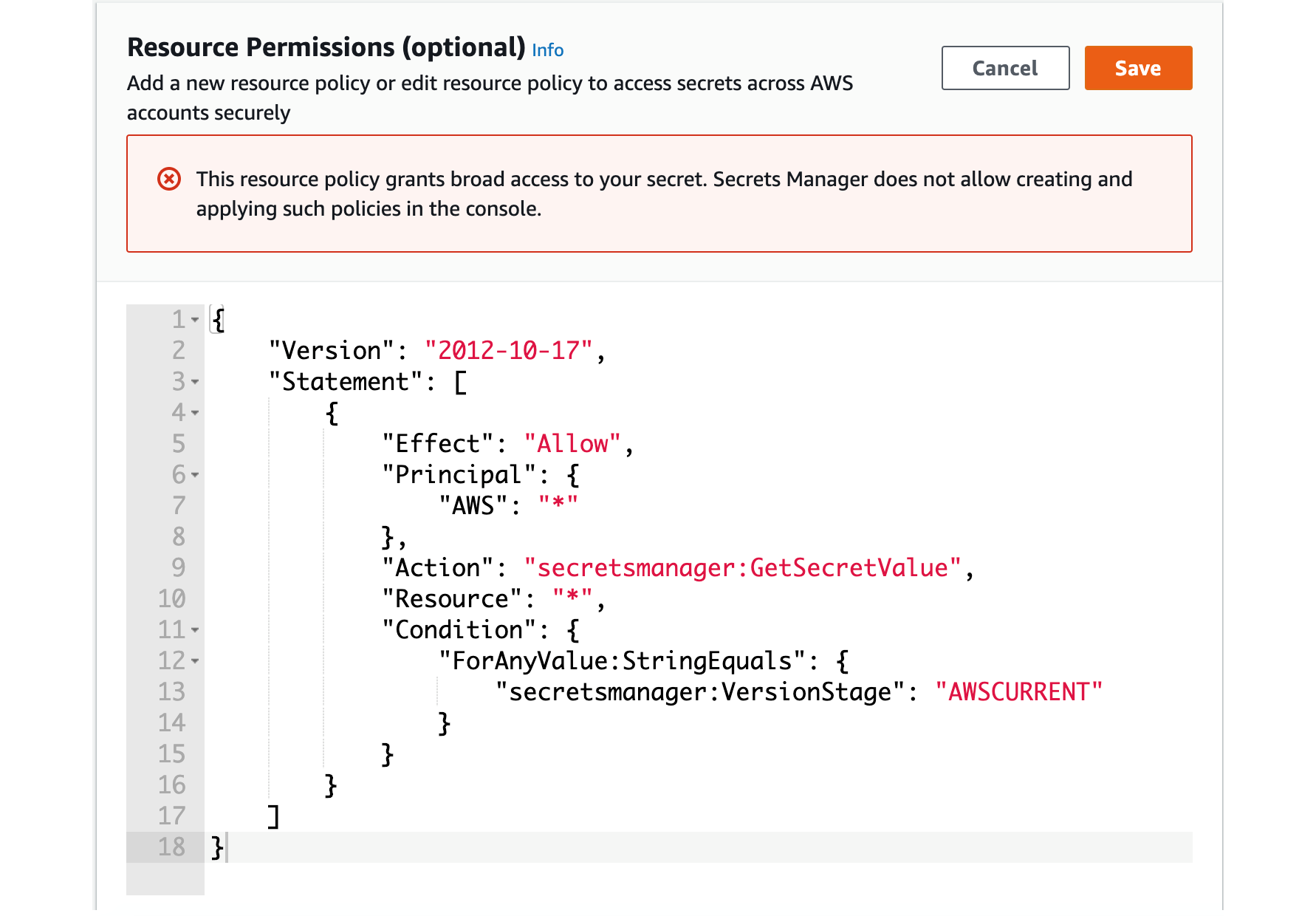
How to use resource-based policies in the AWS Secrets Manager console to securely access secrets across AWS accounts | AWS Security Blog